Information Security made simple in Microsoft Dynamics 365 Business Central
Xtbc Access Manager enables you to enroll all your Microsoft Dynamics 365 Business Central users into Job Roles and to manage your access control in a simple and transparent way.
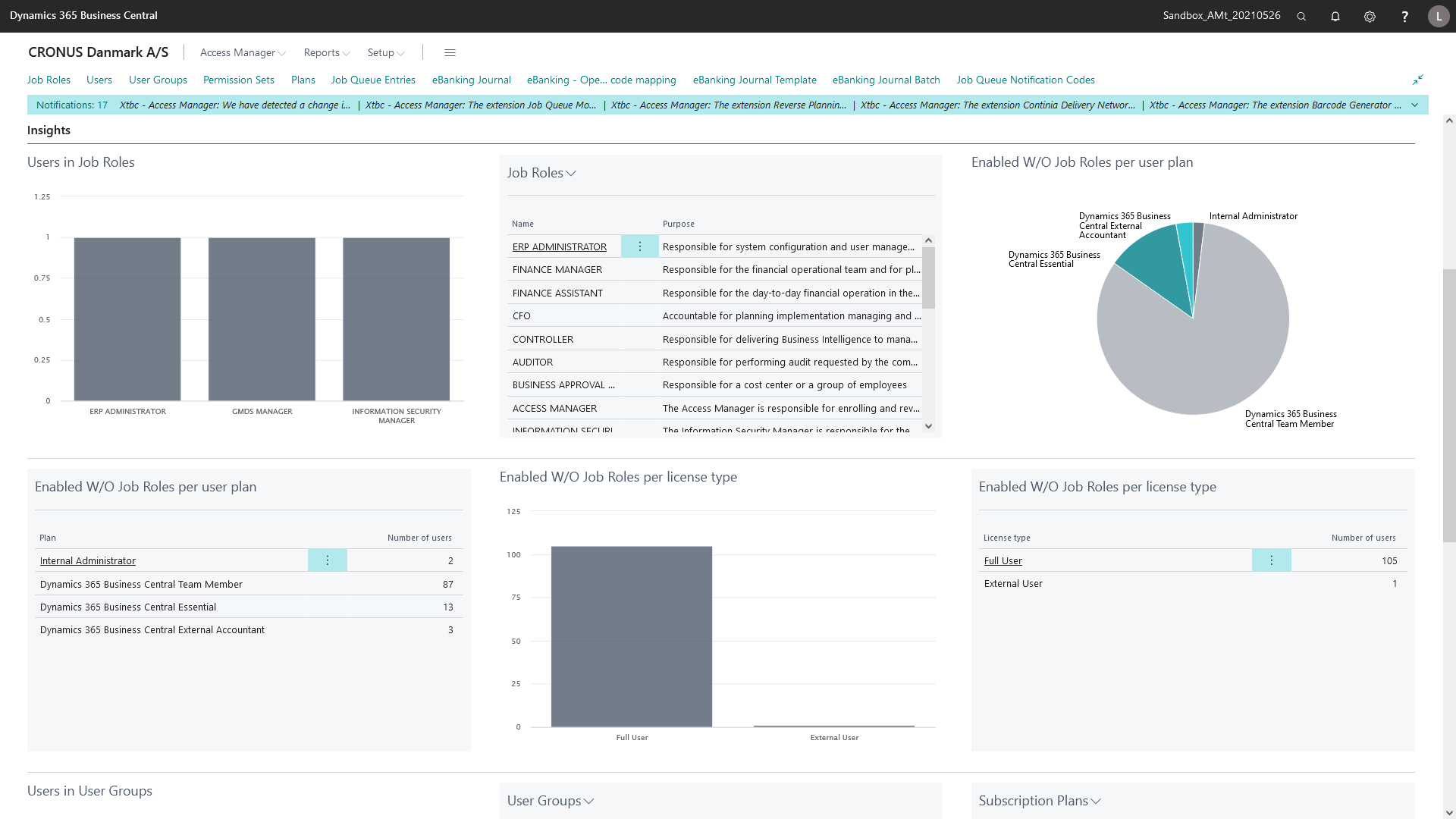
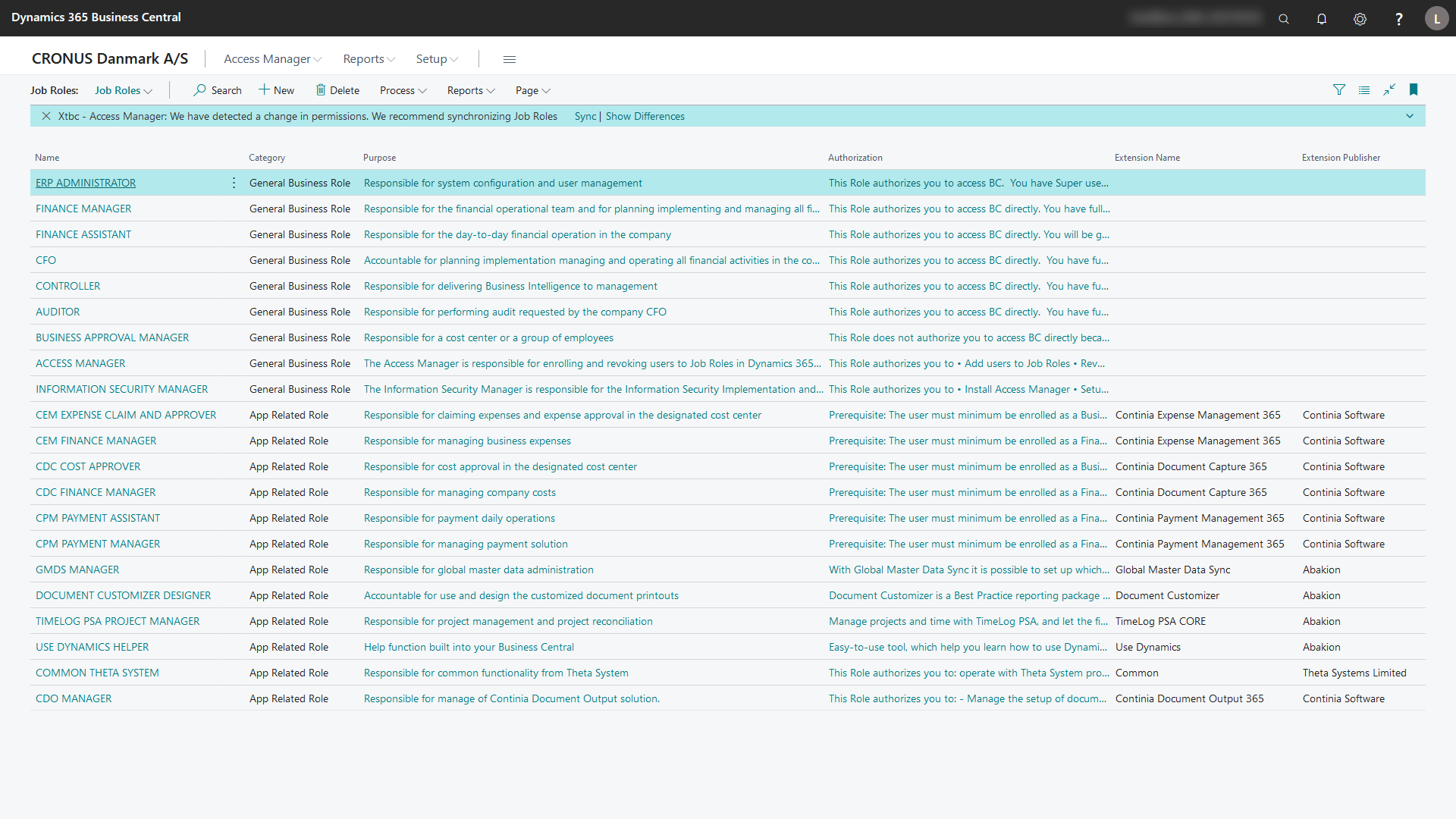
Access Management Center
Your Access Management Center makes it simple for you to authorize and restrict user access in Business Central based on real business roles and responsibilities in your organization.
You can select any Job Roles in your Access Manager and start enrolling users to all the Job Role that equals their business responsibilities.
Key features and benefits
- Authorize user access to Job Roles that equals their business responsibilities
- Revoke or change user access to Job Roles
- Revoke access to BC
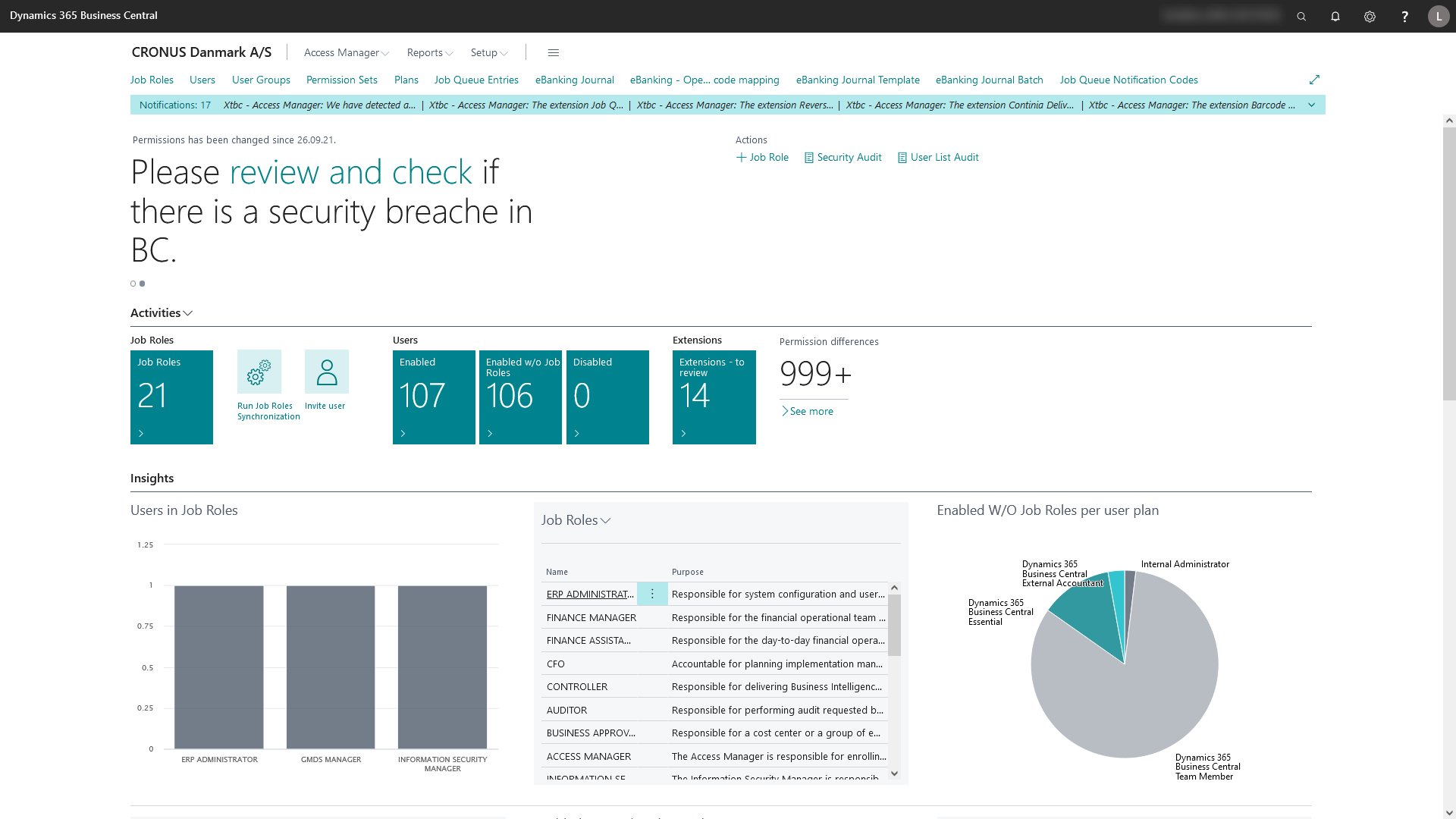
Information Security Center
Your Information Security Center enables you to be proactive and react to any changes of user privileges and system permissions. The interactive interface allows you to dip-dive into permission details to identify changes and to perform the needed security actions.
Key features and benefits
- Identify security breaches related to known and hidden users enabled in BC
- Detect changed permissions
- Ensure no user privileges are broken
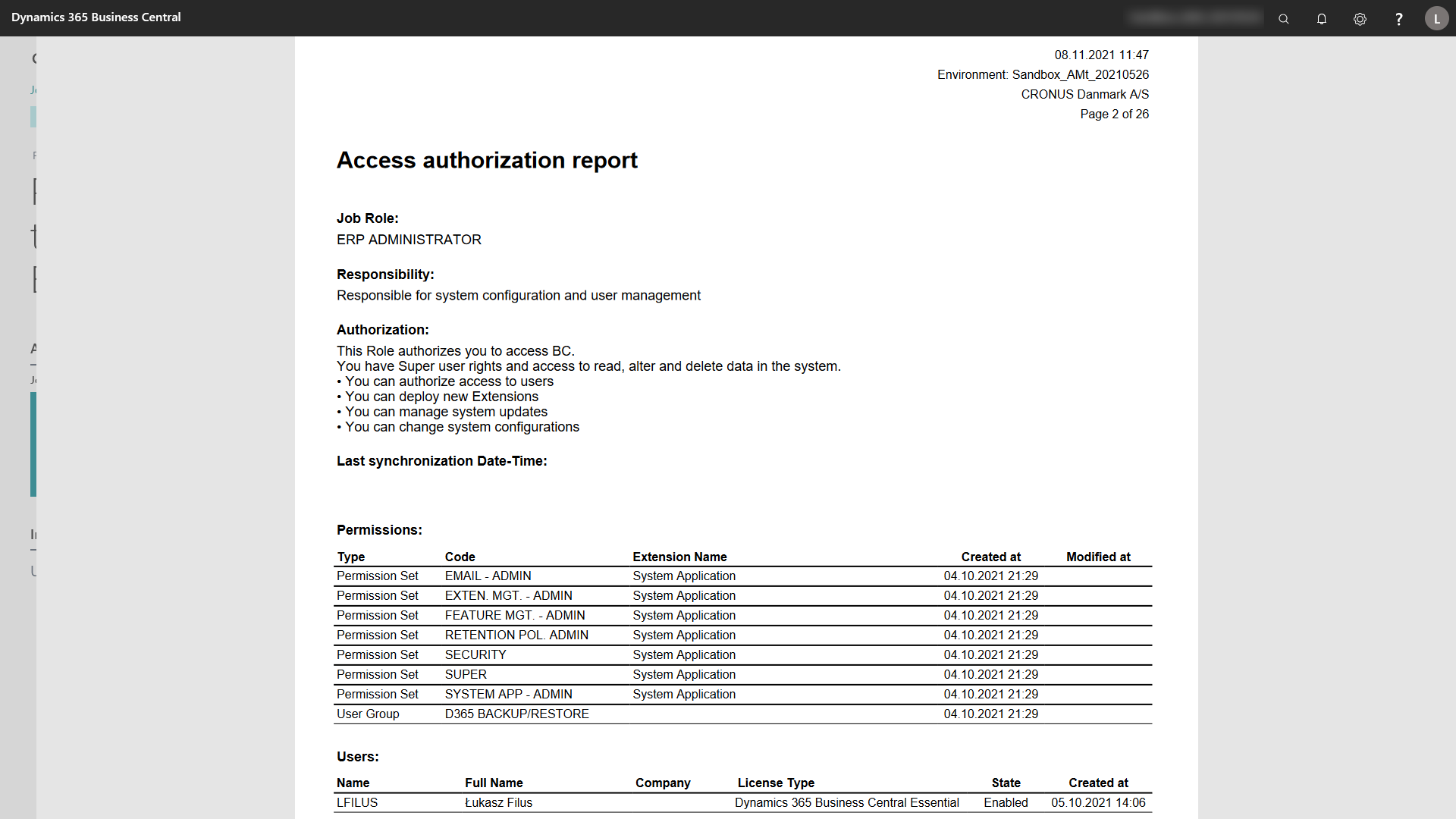
Information Security Report
The Information Security Report delivers audit-ready reporting. Based on the ISO 27001 standard it enables you to meet ongoing compliancy requirements and to reduce the cost for security audits significantly.
The Audit Report detects security and compliance issues including insider abuse policy violations and application availability.
Key features and benefits
- Enterprise Information security Policy
- Distribution list for the Audit Report
- Job Roles
- Responsibility
- Authorization
- System Permission and Permission to App Extensions
- Users, Systems, State, License Type Created and Modified
- List of All Enabled users without Job Roles
- List of All Disabled users
Plans to suit your business
All pricing plans cover all the Information Security essentials, with room to grow. To get started, simply install Xtbc Access Manager from Microsoft AppSource. When your free trial expires, you are asked to subscribe to Xtbc Access Manager in order to continue using the app
Free trial
With a free trial, you can test Xtbc Access Manager and experience the many benefits of using the app. Your free trial expires after 30 days or if you deploy to more than one instant of your company’s accounts in the same environment or into an additional environment in your BC tenant.
99€/month
- 1 Tenant
- 1 Production Environment
- 1 Sandbox Environment
- 1 Production Company
- 1 Evaluation Company
- Unlimited users
- Xtbc Role Templates
149€/month
- 1 Tenant
- 1 Production Environment
- 1 Sandbox Environment
- ∞ Production Companies
- ∞ Evaluation Companies
- Unlimited users
- Xtbc Role Templates
199€/month
- 1 Tenant
- 1 Production Environment
- 1 Sandbox Environment
- ∞ Production Companies
- ∞ Evaluation Companies
- Unlimited users
- Xtbc Role Templates
- Security Filters for Strategic Business Units